BTEC Level 3 Unit 19 Computer Networking Assignment Brief 2026 | Pearson Qualifications
Looking for Plagiarism free Answers for your US, UK, Singapore college/ university Assignments.
| University | Pearson Qualifications |
| Subject | Unit 19 Computer Networking |
BTEC Unit 19 Assignment Brief
| Qualification | Pearson BTEC Level 3 National Extended Diploma in Computing (RQF) |
| Unit No. and Title | Unit 19: Computer Networking |
| Assignment No./ Title | 1 of 2: Investigating Computer Networks |
| Assessor | Ziad Abdelbaky |
| Learning outcome(s) | A: Investigate how computer networks use networking communications protocols to provide effective and secure access to networking services and resources |
| Issue Date | 3/11/2025 | Hand In Date | 4/12/2025 |
Vocational Scenario or Context
You have recently taken a job as a junior network technician for a company that designs and installs networks. The company includes detailed technical information on its website to assist prospective and existing customers.
Task 1
You have been asked to create a page for the company website which covers the following:
- An evaluation of different type of network models (peer to peer, client/server, thin client). You should explain why different types of network, topologies and models are needed and also consider current trends in networking (such as BYOD and cloud computing). Your evaluation needs to be clear and balanced and consider a wide range of aspects including ease of use, ease of set-up, performance and suitability for different applications. You should illustrate your evaluation with examples of how the different network models are suitable for different networking applications covering both benefits and drawbacks.
- An explanation of the characteristics and an analysis of the functions of different networking components used to create different types of networks including LANs, WANs and wireless networks. You need to demonstrate an accurate understanding of the importance of protocols and standards in connecting various types of network. You should illustrate your analysis with examples of how data gets transferred within and between computer networks.
| Checklist of Evidence Required | Completed text and illustrations for the web page
|
| Criteria Covered by this Task: | |
| Unit/Criteria Reference | To achieve the criteria you must show that you are able to: |
| A.D1 | Evaluate different network models and their suitability to meet different client requirements. |
| A.M1 | Analyse the functions of different network components required to construct different network types. |
| A.P1 | Explain the need for different computer network types and models. |
| A.P2 | Explain the characteristics and functions of network components. |
All unit 19 class notes for assignment 1.pdf
Unit 19 assignment 1 feedback .pdf
Flexible Rates Compatible With Everyone’s Budget
Hire a Professional Essay & Assignment Writer for completing your Academic Assessments
Unit 19 Computer Networking Assignment 1
11/11/2025
Introduction
The effectiveness of computer networks in organisations nowadays is to facilitate communication, access to data, and conduct business activities. This project discusses the major network models in current use, such as peer-to-peer, client/server and thin client, examining their advantages, constraints and appropriateness in various applications. It also looks at the impacts of the recent trends, such as BYOD and cloud computing, on the network design. Besides this, the project describes the nature and purpose of vital networking devices applied in LANs, WANs and wireless networks, and the importance of protocols and standards. These insights combined indicate the efficient and secure transfer of data across networks.
Evaluation of Different Network Models and Their Suitability
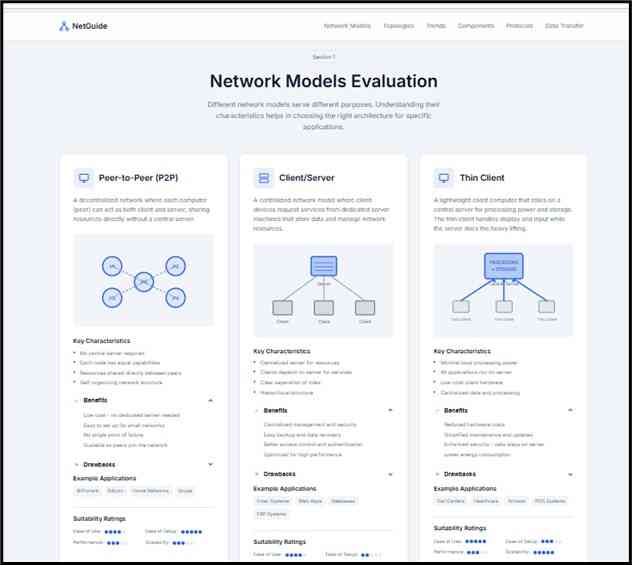
Figure 1: Evaluation of Network Models
The figure contrasts three important models of networks, including peer-to-peer, client/server, and thin client, by indicating how each type responds to various organisational requirements. Peer-to-Peer (P2P) networks also provide easy file sharing with minimal configuration, making it fit in small settings. Client/server networks offer better business operation control, enhanced security and scalability. Thin-client systems ensure increased protection of data through server-side processing and low hardware costs. The figure summarises features, advantages, disadvantages and application examples, and indicates the way performance, usability, as well as maintenance requirements vary. It also indicates how the organisations need to choose the most suitable model by considering the level of work, security requirements and prolonged expansion.
Peer-to-Peer (P2P) Model
The peer-to-peer model is appropriate when there is a need to have simple file sharing and minimal setup. The communication through devices without a central server enables sharing among users within a very short period of time. This renders the model suitable for small locations like small workgroups or temporary computer clusters. It loses its appropriateness, though, when security and performance have to be one of the primary demands. The more devices added, the more traffic and the lower the performance (Reda et al. 2022). Also, it lacks a centralised control, which implies that it is hard to control user access and to secure data. The model can thus only be used with light workloads in the environment.
Client/Server Model
The client/server model applies to the scenarios that entail regulated access, high performance and high security. Accounts, applications and files are managed by a dedicated server, which guarantees a uniform performance despite a large number of users being connected. This is what makes the model appropriate in data-driven workspaces where resources require central management. Its downsides are increased initial work and the expense of achieving professional training levels in staff, but its level of scalability and reliability are the reasons why it is the choice of preference where organised activities are valued.
Thin-Client Model
When it comes to environments requiring secure and standardised access, then thin-client systems would be appropriate. The processing is done on a central server, and the user devices are primarily acting as terminals. This minimises the chances of losing data in local machines and the cost of hardware. The design is suitable in environments that are under control, like training rooms or support centres. The sole weakness is that it is tied to the stability of the servers; should the server go down, then all the terminals connected cease to work.
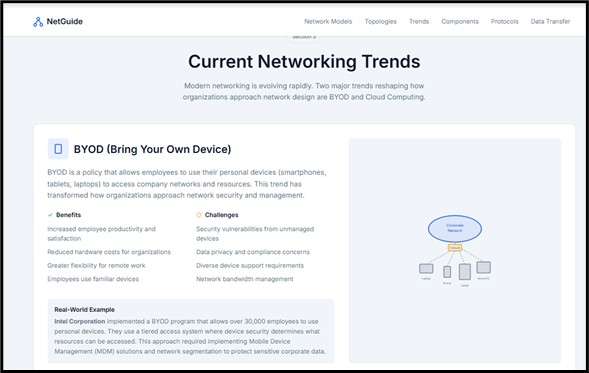
Suitability in Light of Current Trends
The choice of the models of the network depends on the modern tendencies. BYOD environments need to have robust authentication, compatibility management and access policies. These needs are better met by the use of thin clients and client/server networks as opposed to peer-to-peer systems. Cloud computing transfers the applications and storage to external premises, hence networks should have the capabilities of interlinking with the cloud facilities in a safe manner (Saldarriaga-Zuluaga et al. 2021). This requirement is more efficiently addressed with client/server and thin-client models, which offer centralised control of policy and secure channels of communication.
Need for Different Computer Network Types and Models
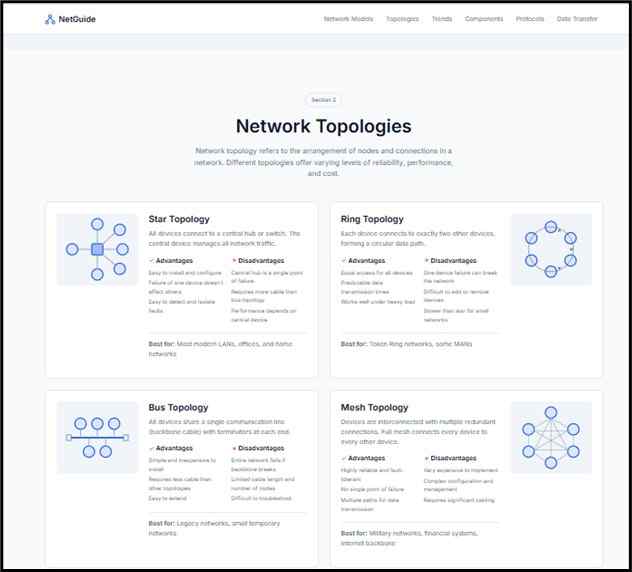
Figure 2: Different Types of Network Topologies
This figure shows that there are four major topologies of networks, namely: star, ring, bus and mesh and the influence each topology has on performance, reliability and cost is explained. Star topology is among the most commonly used topologies because it is highly performing, and faults are easy to isolate. Ring topology allows data to flow systematically; however, it is stopped by a failure (Saba et al. 2022). Bus topology is cheap and easy to construct; however, it has drawbacks in terms of collisions and low scalability. Mesh topology is very redundant and highly reliable, which is applicable to mission-critical systems. The diagram explains why organisations require various topologies based on the size of the network, the performance requirement and fault-tolerance requirement to aid in making decisions during the design of the current LANs and WAN infrastructures.
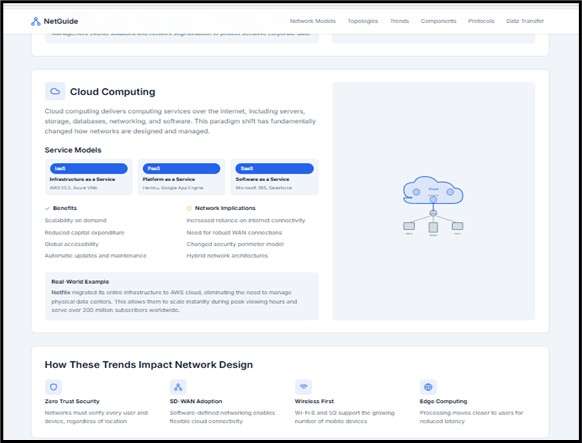
Figure 3: Current Networking Trends
This figure explains two significant trends that define the design of modern networks, which are BYOD (Bring Your Own Device) and cloud computing. BYOD makes employees more flexible and productive since they are able to use their own devices, yet it creates security, management and compatibility issues. Cloud computing is a disruptive technology that is changing the way organisations store, process and access data through services such as IaaS, PaaS and SaaS, and it is scalable and less expensive to run. The diagram presents the impact of such trends on authentication, access control, bandwidth planning and data protection. Collectively, they illustrate the imperative that requires flexible, secure and policy-based network designs that provide support to the current mobile workforce and cloud-based processes.
Differences in Scale and Coverage
There are various types of computer networks due to the different sizes of physical operations of organisations and the environment. LANs are engineered to support small areas like offices, residential, laboratory or classrooms where the devices need to be capable of communicating fast within a small area (within the office or home). On the other hand, Wide Area Networks (WANs) are spread across cities, countries or even worldwide, and thus different branches or remote servers can be linked. Such differences in scale and functionality are necessary since not all types of networks can be used to support all operational needs. These high velocities, costs, and infrastructure to support both small and large environments vary greatly, hence the need to have different types of networks.
Variation in Performance Requirements
There are also needs of performance needs that lead to the requirement of various types of networks. LANs focus on fast data transmission over a limited space that is essential in activities such as file transfer, local applications and communication, among others. WANs are, however, designed to handle data transfer over a long distance and are concerned with the stability, routing effectiveness and secure communication between the endpoints located at a distance. Wireless networks are particularly necessary where mobility is necessary, such as in places such as retail floors, campuses, hospitals, and contemporary offices (Korashy et al. 2023). They do away with the constraint of cabling and enable devices to dynamically connect. The performance requirements of speed, reach, or mobility lead to the need to use different network structures.
Need for Different Network Models
The network models vary in that many situations require varying degrees of complexity, cost, security and manageability. P2P networks are suitable in scenarios where simplicity and low cost is of paramount importance, as is the case in small home systems. They enable devices to communicate directly with one another without a centralised server. Conversely, client/server networks are critical to organisations where central management is required, security is mandatory and scalability is needed. The further extension of this structure is due to thin-client models, whereby a majority of the processing is done in central servers, thereby enhancing control and making maintenance easier. The availability of more than one model gives a network designer an opportunity to select a structure that meets their workload, budget and security needs.
Impact of Different Topologies
Prime examples of topologies include star topologies, ring topologies, bus topology and mesh topology since each has its advantage with different objectives in networking. Star topologies give isolation of faults and simple troubleshooting. Ring topologies provide predictability in performance when there is consistency in the load. Bus topology costs less to install small, simple networks, whereas mesh topologies provide high redundancy and resilience under all possible conditions. These alternatives enable networks to be constructed either based on certain priorities, including reliability, cost-efficiency or performance.
Influence of Modern Trends
The modern tendencies contribute to the necessity of alternative types and models of networks as well. BYOD communities are based on the openness of wireless communication and robust authentication networks. The networks needed in cloud computing encompass remote resources, applications that are virtualised and bandwidth that can be scaled. This emerging trend necessitates the fact that there is no single type of network that is adequate. Rather, a combination of models and topology is the one that ensures that the requirements of modern communication are met entirely.
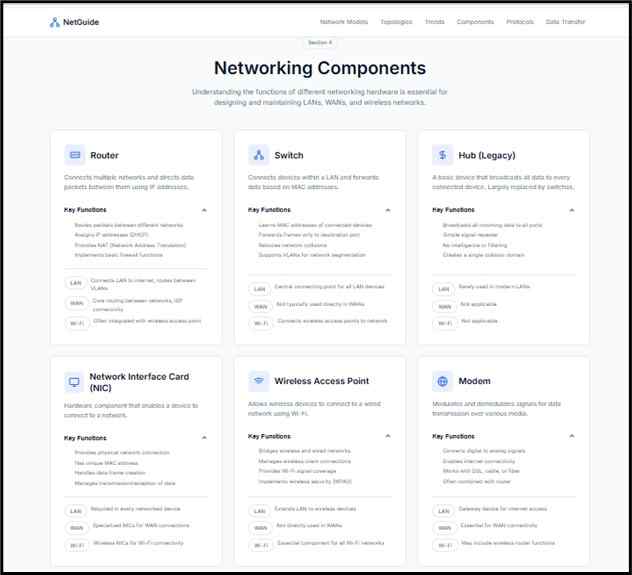
Analysis of Functions of Different Network Components for Different Network Types
Figure 4: Functions of Networking Components Based on Networking Types
This figure describes the applications of key networking elements that are applicable in LAN, WAN and wireless networks. Routers, switches, hubs, NICs, modems and wireless access points have different functions in the transmission of data. Switches are used to control traffic in LANs, and routers are used to route packets between networks. Wi-Fi is connected with the help of wireless access points, and devices can communicate with the help of NICs over both wired and wireless networks (Vala et al. 2023). Modems have the capability of supporting WAN connections through the conversion of digital and analogue signals. The diagram depicts the interaction between these items to form dependable network infrastructures, which promote effective communication and facilitate organisations to achieve performance, coverage and connectivity objectives.
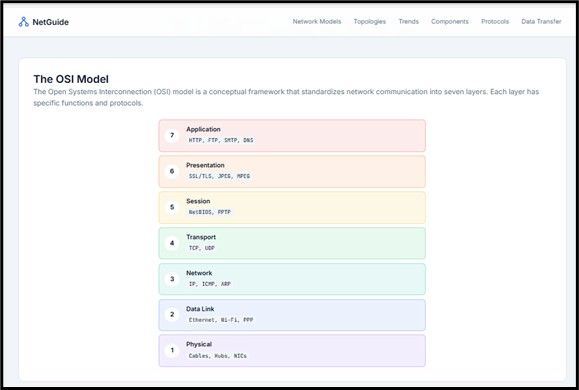
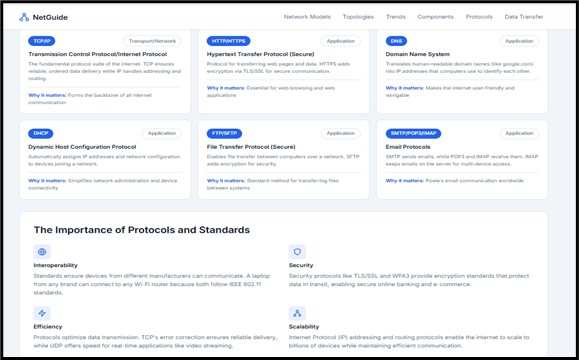
Figure 5: Importance of Protocol and Standards
This figure shows the role of protocols and standards in interoperability and trustworthy interaction of different devices and networks. It has examples of HTTP, FTP, DHCP, DNS, TCP/IP and email protocols demonstrating how each of them attends certain networking functions. The OSI model illustrated explains the flow of data in the process of layered functions in which layers offer fundamental services, which include routing, encryption, addressing and error handling (Yathiraju, 2022). The diagram underlines the necessity of standardisation to establish compatibility, security and effective data transfer between LANs, WANs and wireless systems. Universal rules are protocols that ensure the networks are usable, scalable and able to serve to link systems all over the world.
Switches are considered to be at the centre of the work of Local Area Networks (LANs): they regulate the passage of data frames through the network by devices that are interconnected. Switches, unlike hubs, do not transmit all the data to all the connected devices, but instead, with the help of MAC address tables, send the frames to the destination to which the device is supposed to be connected. This directional forwarding has a considerable amount of performance improvement, decreases collisions and better the efficiency of the network (Hong et al. 2021). Switches are used in offices, schools, or small businesses to guarantee that in-office communication is quick, dependable, and does not slow down as the number of connected devices increases.
Routers in Inter-Network Communication
Routers enable communication across different networks by determining the most efficient path for packets. They rely on IP addressing and routing protocols such as OSPF or BGP to make forwarding decisions. In Wide Area Networks (WANs), routers connect geographically distributed sites, branch offices, and remote servers. They also facilitate access to cloud platforms by directing outgoing and incoming traffic between local networks and external service providers (Saldarriaga-Zuluaga et al. 2021). Without routers, devices would be unable to communicate beyond their local subnet, making them essential to any organisation requiring internet or multi-site connectivity.
NICs as Access Interfaces
NICs are responsible for connecting a device to a network. A data transmission is allowed between wired and wireless via them, which transform internal data to electrical or optical or radio signals that could be transmitted. All devices, such as desktops, servers, printers, or smartphones, need a NIC to connect to the network resources. Unique MAC addresses are also written on the NICs, which assist switches and routers in determining the accurate device. In a current-day network, NICs facilitate such advanced features as duplex communication and high-speed standards, which ensure that there are no delays in the flow of data inside the system.
Wireless Access Points in WLANs
Wireless Access Points (WAPs) are devices that expand the network connectivity to the wireless devices with the aid of radio frequencies. They serve as central communication points in WLANs, enabling laptops, mobile devices and IoT devices to use network services without physical connections. WAPs facilitate mobile and mobile operations in workplaces, where they are adopted under the policy of Bring Your Own Device (BYOD). They further recognise the security standards, including WPA3, which would guarantee encryption of wireless traffic and protection against intrusions (Zellagui et al. 2024).
Modems in WAN Connectivity
Modems are devices that allow local networks to interface with long-distance networks by enabling analogue signals aggrieving a digital device to be converted into digital signals that can be transmitted over telephone lines, fibre lines, or cable lines. They play a fundamental role in creating internet connectivity and really creating WAN connections between distantly located sites.
Combined Function in Network Types
The various types of networks depend on the combination of different elements to work successfully. LANs mostly rely on switches to manage the internal traffic, whereas WANs demand routers and modems to manage communication between them and the new location(s). Wireless networks are based on the use of access points and wireless NICs to facilitate mobility and coverage. All of these elements make up networked systems which underpin local operation, remote connectivity and cloud integration.
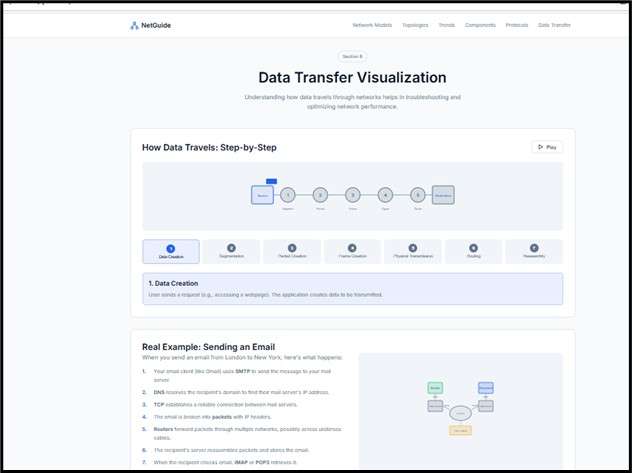
Characteristics and Functions of Network Components
Figure 6: Data Transfer Demonstration with a Real-World Example
The figure is used to depict the sequence of data transfer in the process of sending an email. It demonstrates the creation of data, its encapsulation, separation and transmission over the OSI layers and their travel over the network. The diagram describes the processing of packets by routers, switches and servers, which ensures the packets reach the right destination. It also monitors mistake examination, working with and protocol inclusion during the trip. The example helps to understand the abstract concepts of networking better by associating them with the daily use of digital communication. In general, the example shows that the transfer of data in an efficient and structured manner is the foundation of good internet and organisational communications.

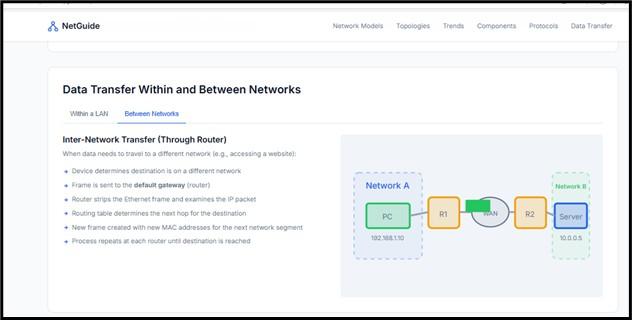
Figure 7: Data Transfer within a LAN and between Networks
This figure is a comparison between the transfer of data within a LAN and across networks. The LAN example demonstrates the manner in which frames pass through switches based on MAC address, after Layer 2 operations, in order to achieve effective local communication. The inter-network example shows that IP addresses are used by routers to send packets between networks, which interact with remote devices. It brings out routing decisions, address translation and protocol involvement (Javed et al. 2022). The example supports the notion of the significance of the knowledge of local and wide-area communication processes, since organisations need to have smooth information exchange to cope with their internal affairs and external connectivity. This analogy illustrates the collaboration and interrelation of elements and protocols to provide efficient transmission of reliable data.
Switch Characteristics and Functions
Switches work in Layer 2 of the OSI model, implying that the MAC addresses are utilised to forward the frame to the destination device. They can inspect MAC tables and therefore reduce unnecessary broadcasting, minimising collisions throughout the network. This selective forwarding increases the performance level in general, and switches are central to the effective LAN settings. They facilitate full duplex communications, segmentation of VLANs and better bandwidth control, which allows the efficient internal data flow in even networks with many attached devices.
Router Characteristics and Functions
Routers work on Layer 3 and do a forwarding of packets within distinct IP networks. Their most important purpose is in determining the path- routing tables and protocols (OSPF, RIP or BGP) are used to estimate the most efficient path that data should follow. Network address translation (NAT) and firewall filtering, and traffic management are also carried out by routers, and therefore, these are vital in secured and regulated communications outside of a single network. Routers guarantee the delivery of data to the right destination off the LANs when connecting LANs to WANs, linking branch offices, or getting access to cloud services.
NIC Characteristics and Functions
NICs represent the key physical and logical point of access of a device to a network medium. NICs do the translation of device data to electrical, optical or wireless transmissions. They include individual MAC addresses to be identified with, frame data, and also support duplex configurations and negotiation of the speed. Current NICs can support innovations like WIFI 6, gigabit Ethernet or virtualisation offloading, and the devices enable them to be relevant in the wired and virtual network.
Modem Characteristics and Functions
The modems are used to shape the digital signals into analogue forms so that they can be transmitted over telephone communication lines or cable or fibre-based communication lines before being demodulated once more to digital data. This conversion is necessary when long-distance connections are required, where the internal networks can connect to the external infrastructures, like the internet or WAN services. Local networks would not have the ability to connect across the public or broadband networks without modems.
Wireless Access Point Characteristics and Functions
Wireless Access Points give devices the capability of being connected to the network by as much as radio frequencies in lieu of the real physical cables. They also handle user authentication, signal distribution, and channel allocation to stabilise wireless coverage. The encryption levels, such as WPA2 and WPA3, are supported by its access points, and thus, mobile connectivity is secure (Alamshah et al. 2024). They are essential in the fields where mobility is needed, like BYOD offices, campuses or open areas.
Protocols and Standards
The use of protocols like TCP/IP, DNS, DHCP and HTTP establishes guidelines on how to address, format and relay data on the networks so that communication proceeds effectively. Organisations such as IEEE and ISO have created standards that match other devices produced by different companies. OSI model can be used to offer a layered model on how data is encapsulated, transmitted and processed by components in ensuring there is predictable network behaviour and interoperability.
Conclusion
This project has shown the importance of network design depending on the knowledge of various models, topologies, components, and communication standards. When comparing peer-to-peer, client/server, and thin-client architectures, along with the more important topologies and recent developments such as BYOD and cloud computing, it is obvious that not a single approach would be effective in all organisations. The analysis of networking hardware, procedures of transferring protocols and data further brings out the significance of reliability, security and interoperability. In general, effective networks must be planned, as the technologies and standards applied must be used to ensure efficient, scalable, and secure communication both inside and between current digital systems.
References
Alamshah, A., Ramli, S.P., Mansor, N.N., Usama, M., Mokhlis, H., Suyono, H. and Hasanah, R.N., 2024. Recent developments of directional overcurrent relay coordination in ring distribution network based on hybrid optimisation techniques. IEEE Access.
Hong, L., Rizwan, M., Wasif, M., Ahmad, S., Zaindin, M. and Firdausi, M., 2021. User-defined dual setting directional overcurrent relays with hybrid time current-voltage characteristics-based protection coordination for active distribution network. Ieee Access, 9, pp.62752-62769.
Javed, A.R., Ahmed, W., Alazab, M., Jalil, Z., Kifayat, K. and Gadekallu, T.R., 2022. A comprehensive survey on computer forensics: State-of-the-art, tools, techniques, challenges, and future directions. IEEE Access, 10, pp.11065-11089.
Korashy, A., Kamel, S. and Jurado, F., 2023. Optimisers for optimal coordination of distance relays and non-standard characteristics of directional overcurrent relays. Electrical Engineering, 105(6), pp.3581-3615.
Reda, A., Abdelgawad, A.F. and Ibrahim, M., 2022. Effect of non-standard characteristics of overcurrent relay on protection coordination and maximising overcurrent protection level in distribution network. Alexandria Engineering Journal, 61(9), pp.6851-6867.
Saba, T., Rehman, A., Sadad, T., Kolivand, H. and Bahaj, S.A., 2022. Anomaly-based intrusion detection system for IoT networks through deep learning model. Computers and Electrical Engineering, 99, p.107810.
Saldarriaga-Zuluaga, S.D., López-Lezama, J.M. and Muñoz-Galeano, N., 2021. Adaptive protection coordination scheme in microgrids using directional over-current relays with non-standard characteristics. Heliyon, 7(4).
Saldarriaga-Zuluaga, S.D., López-Lezama, J.M. and Muñoz-Galeano, N., 2021. Hybrid harmony search algorithm applied to the optimal coordination of overcurrent relays in distribution networks with distributed generation. Applied Sciences, 11(19), p.9207.
Vala, T.M., Rajput, V.N. and Al‐Sumaiti, A.S., 2023. Investigating the performance of non‐standard characteristics‐based overcurrent relays and their optimum coordination in distributed generators connected networks. IET Generation, Transmission & Distribution, 17(13), pp.2978-2995.
Yathiraju, N., 2022. Investigating the use of an artificial intelligence model in an ERP cloud-based system. International Journal of Electrical, Electronics and Computers, 7(2), pp.1-26.
Zellagui, M., Belbachir, N., Amroune, M. and El-Bayeh, C.Z., 2024. Investigating the performance of non-standard overcurrent relay with integration of photovoltaic distributed generation in power distribution system. Periodica Polytechnica Electrical Engineering and Computer Science, 68(1), pp.27-36.
Flexible Rates Compatible With Everyone’s Budget
Hire a writer to get plagiarism free assignment answers of this question
Looking for Plagiarism free Answers for your US, UK, Singapore college/ university Assignments.